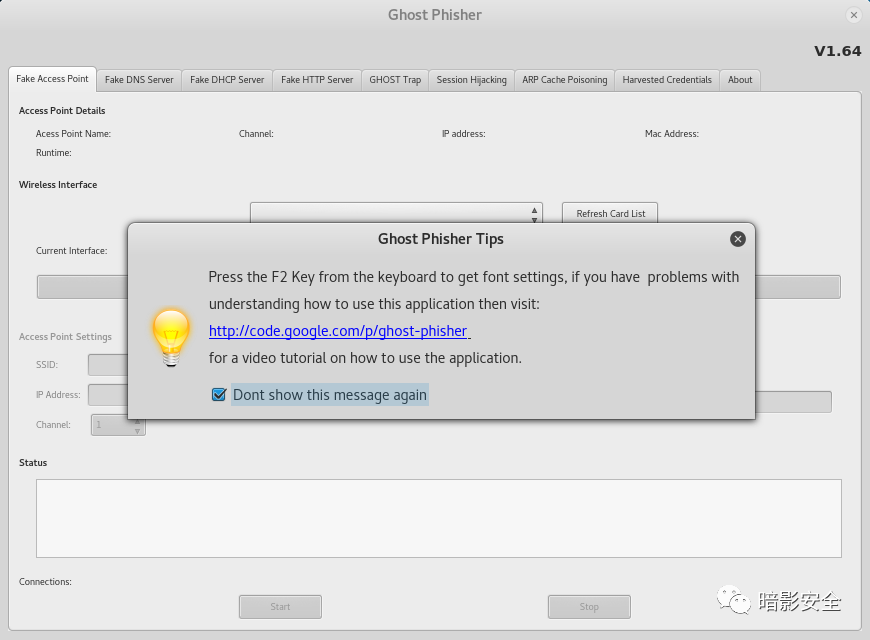
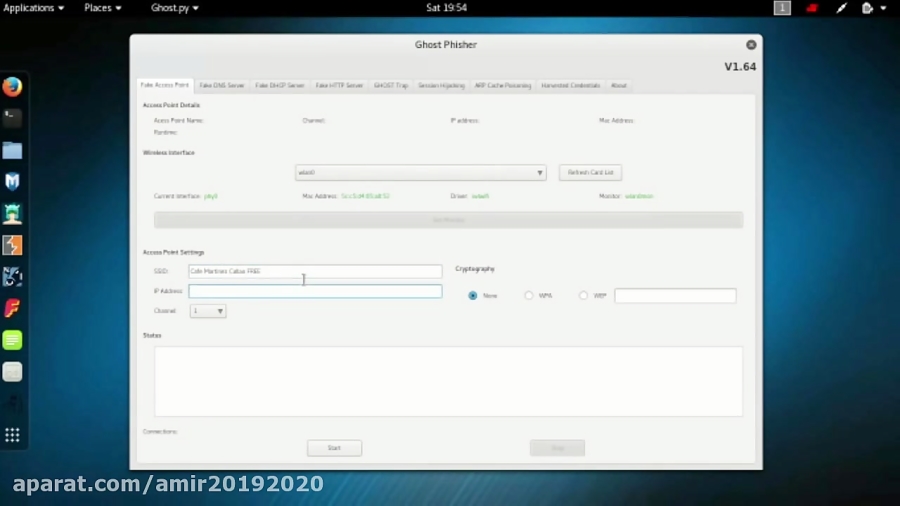
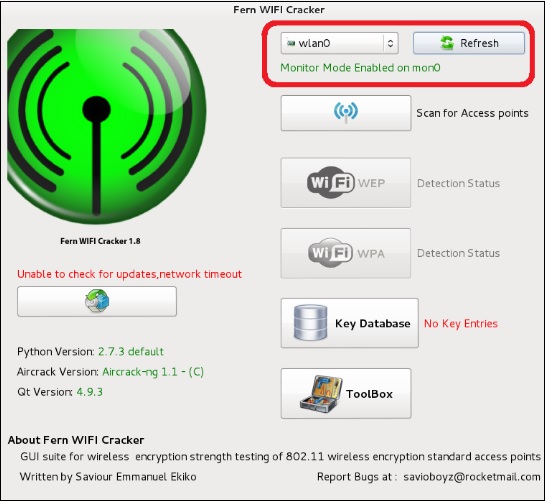
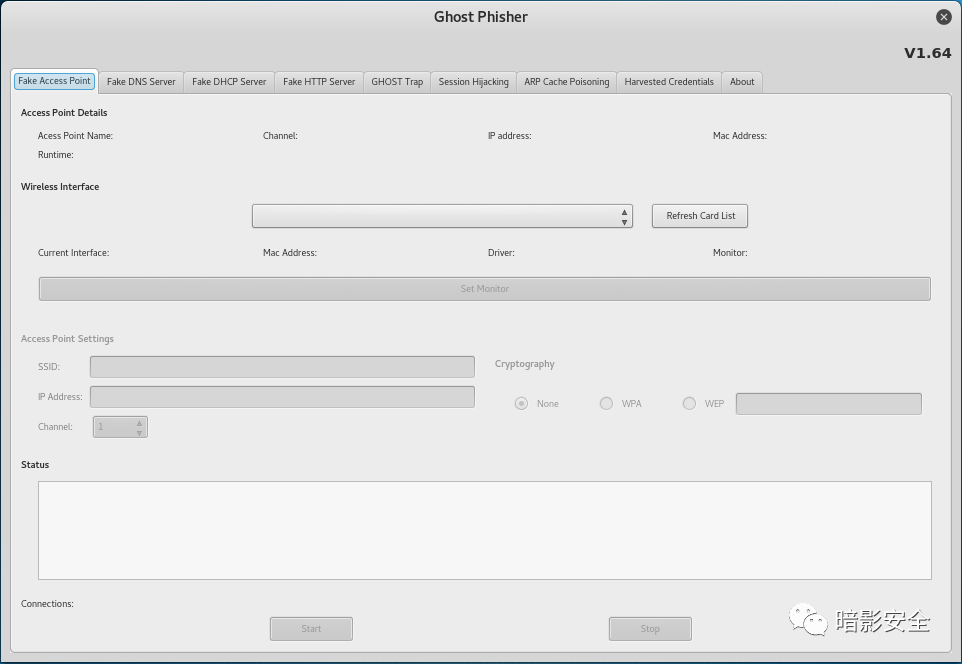
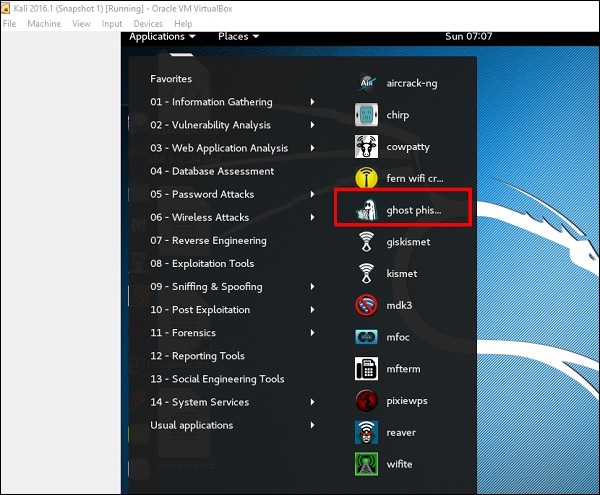
How to create fake wifi hotspot (ghost phisher) using kali linux 2 - Microsystem Hotspot | wifi marketing | internet management | wifi solutions | selling internet packages | social wifi | Mikrotik controller
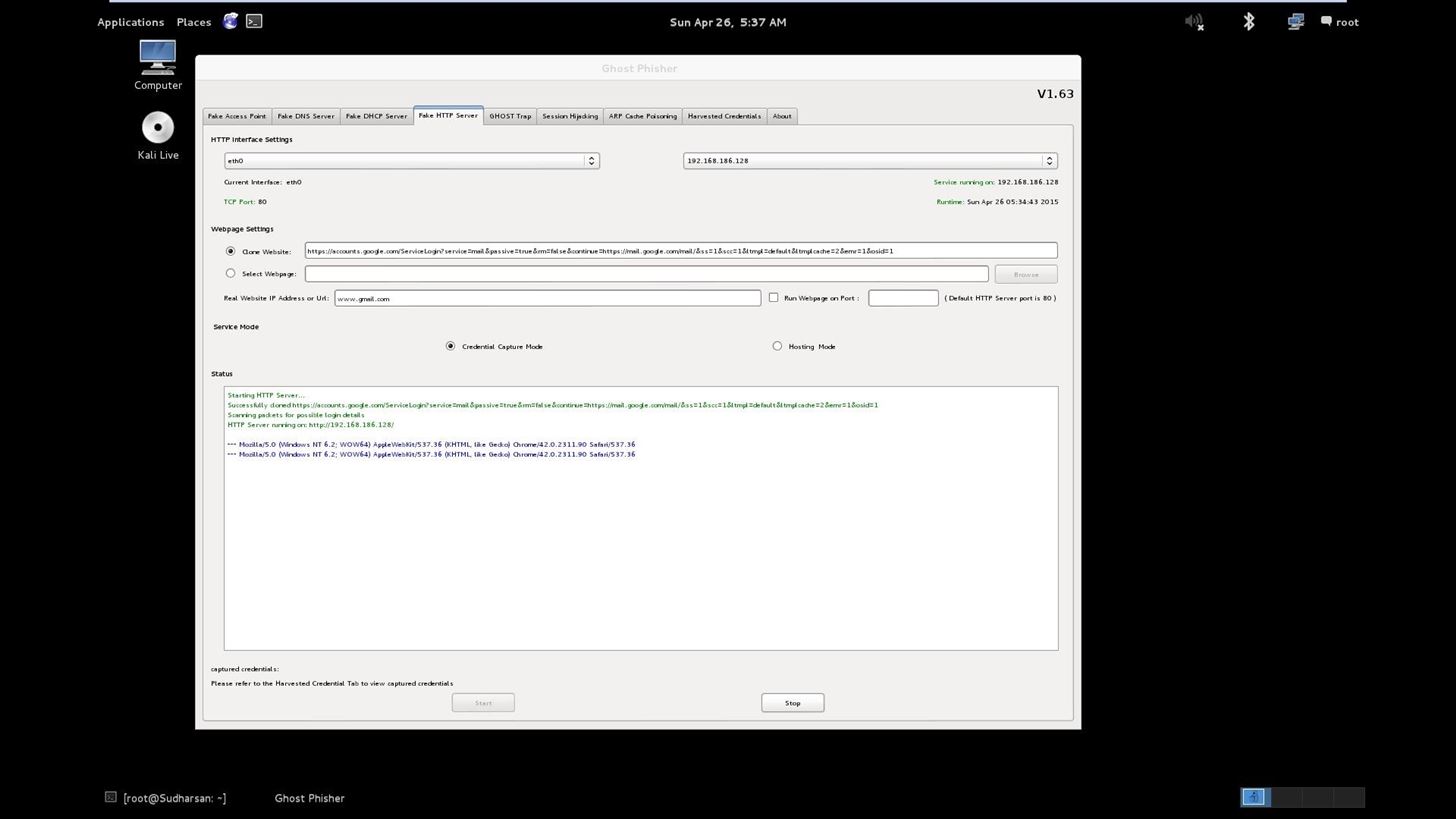
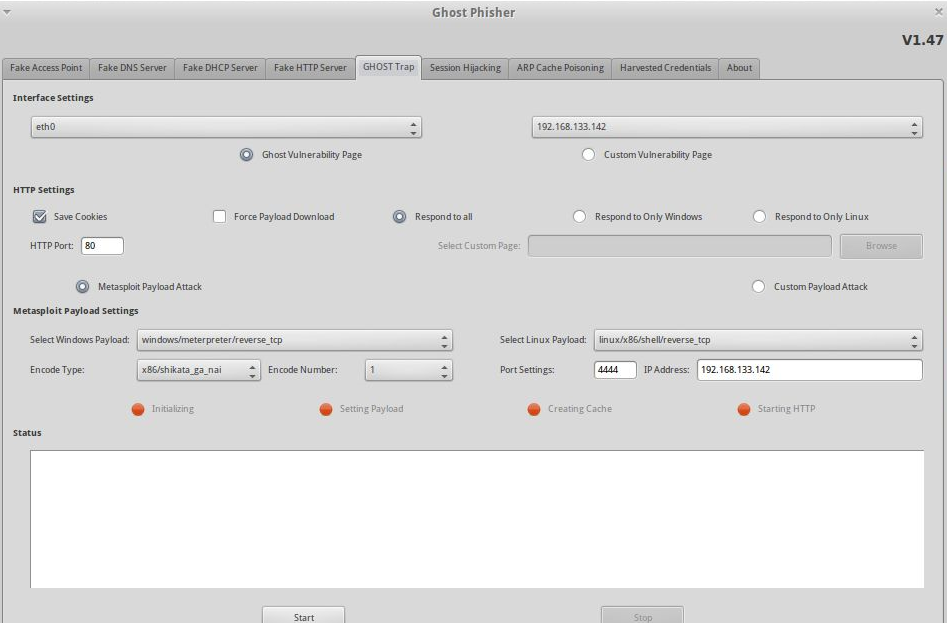
![Working with Ghost Phisher - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book] Working with Ghost Phisher - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781787120235/files/assets/f9a4492c-dd5e-421e-8b0d-6face753d97e.png)
Working with Ghost Phisher - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book]





![Ghost Phisher v1.5] GUI suite for phishing and penetration attacks Ghost Phisher v1.5] GUI suite for phishing and penetration attacks](http://2.bp.blogspot.com/-9Z93jnb5M7k/UsM-961nN1I/AAAAAAAABgY/WIEhuWGVYpA/s1600/ghost_phisher.png)





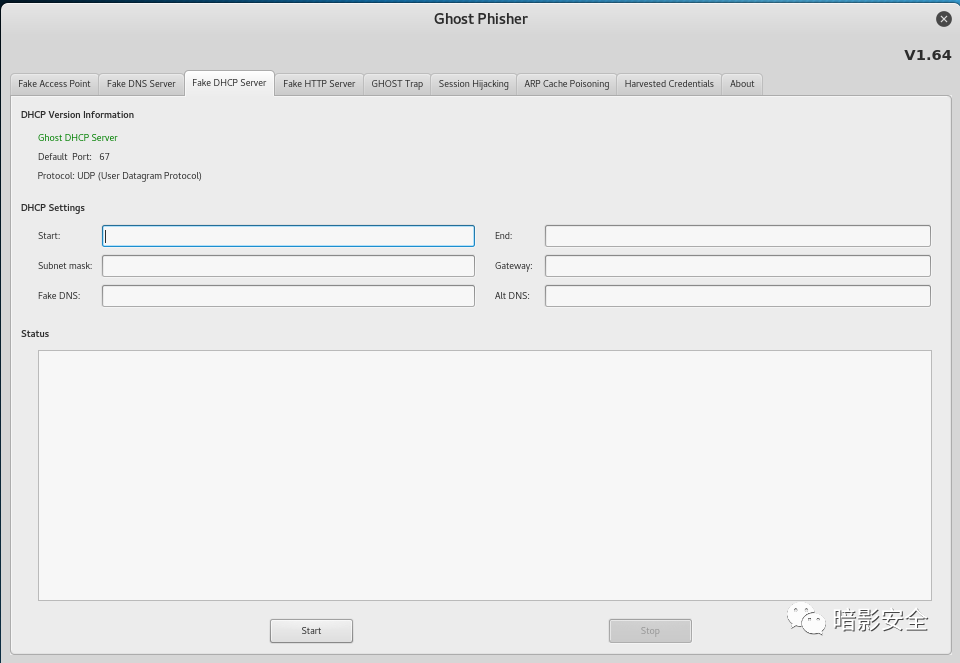
![Ghost-Phisher - Havest Credentials [Kali Linux] - YouTube Ghost-Phisher - Havest Credentials [Kali Linux] - YouTube](https://i.ytimg.com/vi/WUG89n0m_jM/maxresdefault.jpg?sqp=-oaymwEmCIAKENAF8quKqQMa8AEB-AH0CYAC0AWKAgwIABABGBMgQih_MA8=&rs=AOn4CLDwkA7yg-QDtkiiLN8DHyTY-I6DGw)