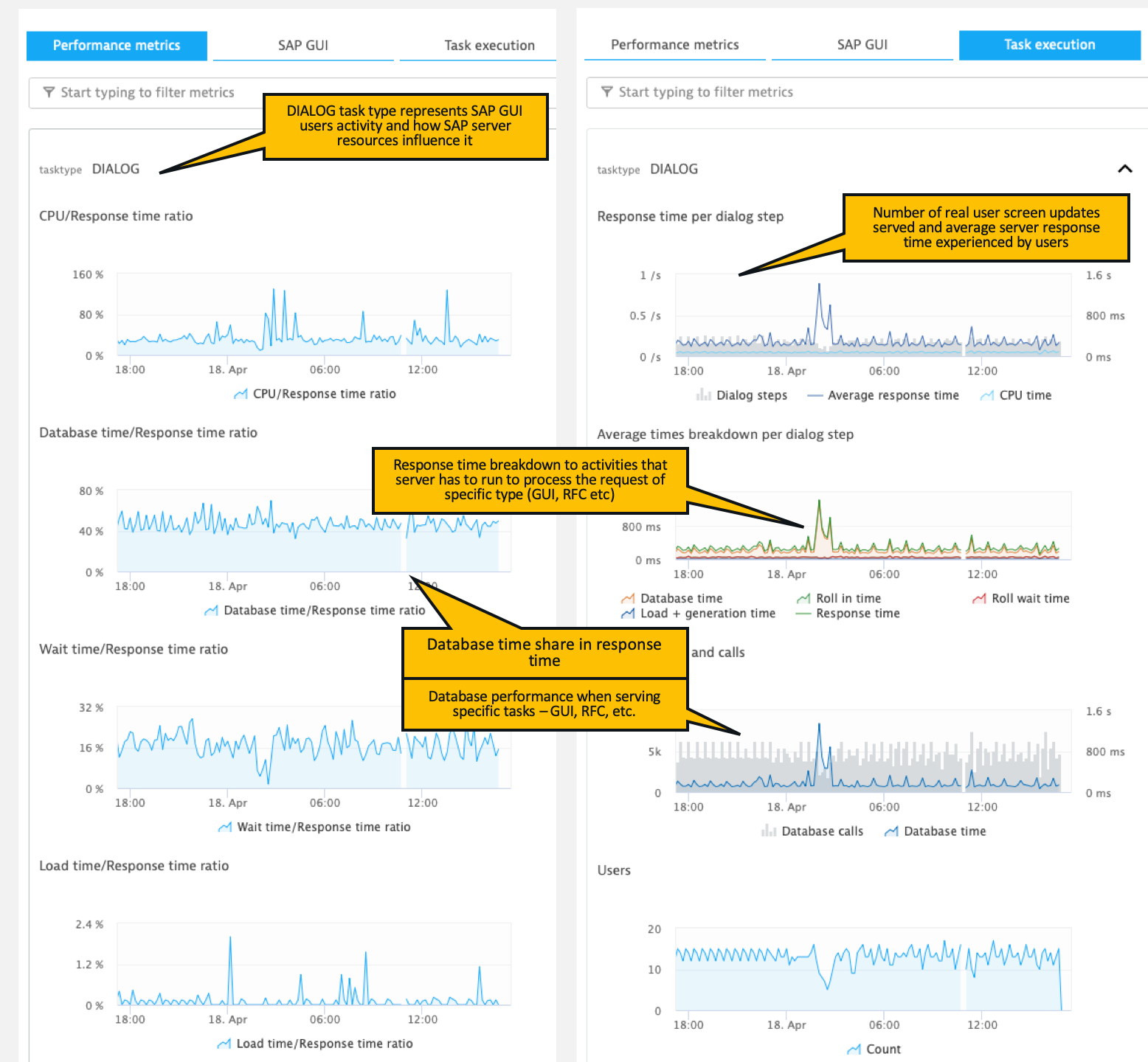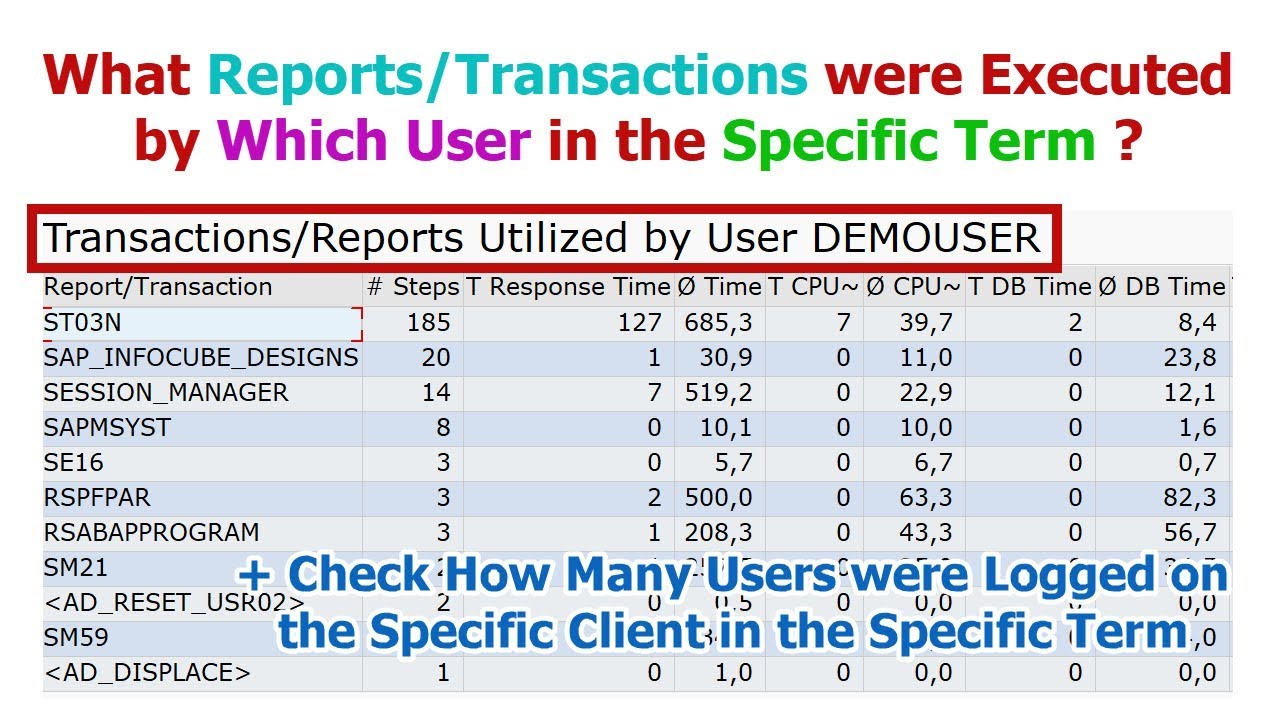
SAP: Finding Reports/Transactions Executed By the Specific User in the Specific Term (in ST03N) - YouTube

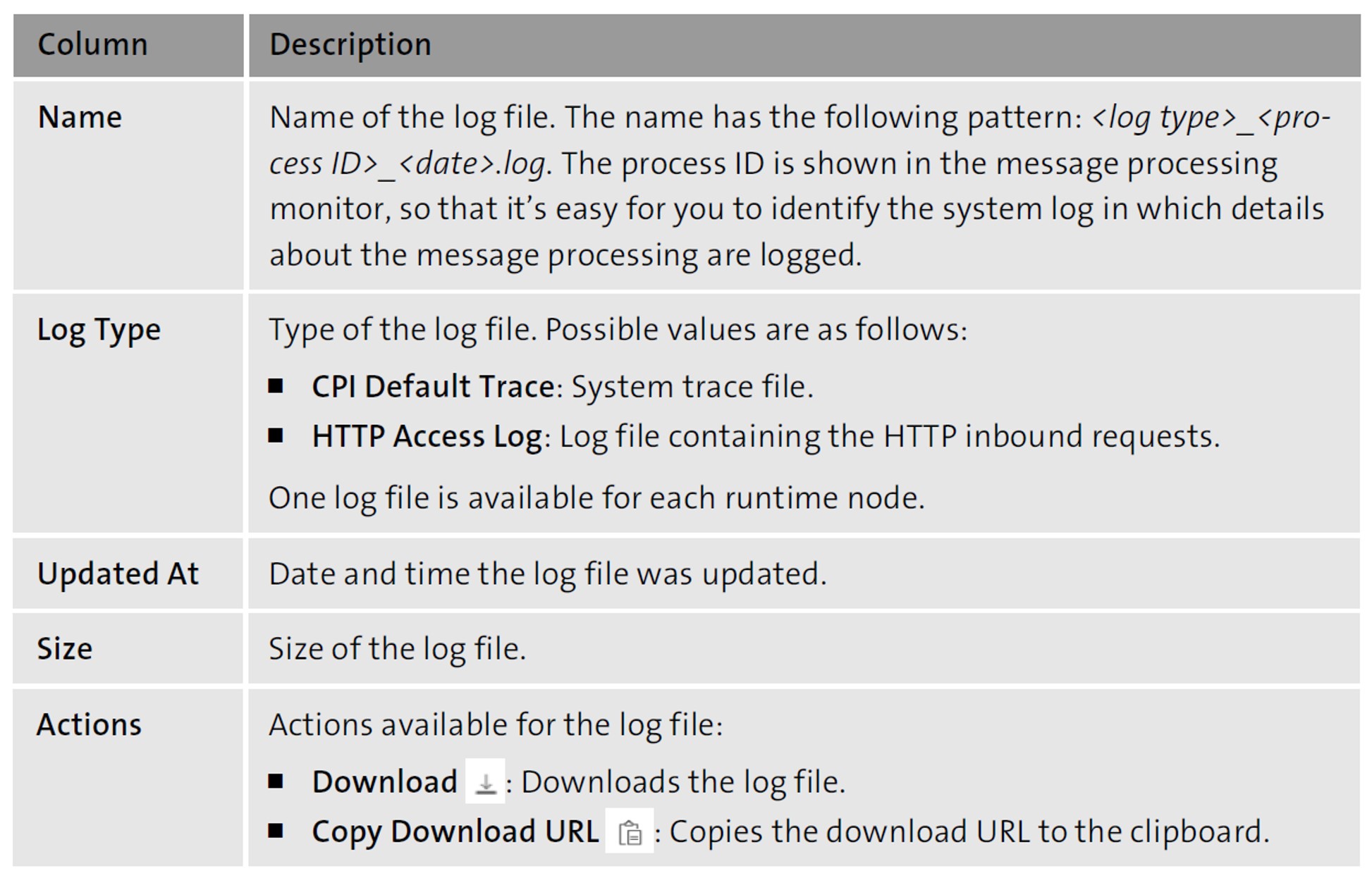
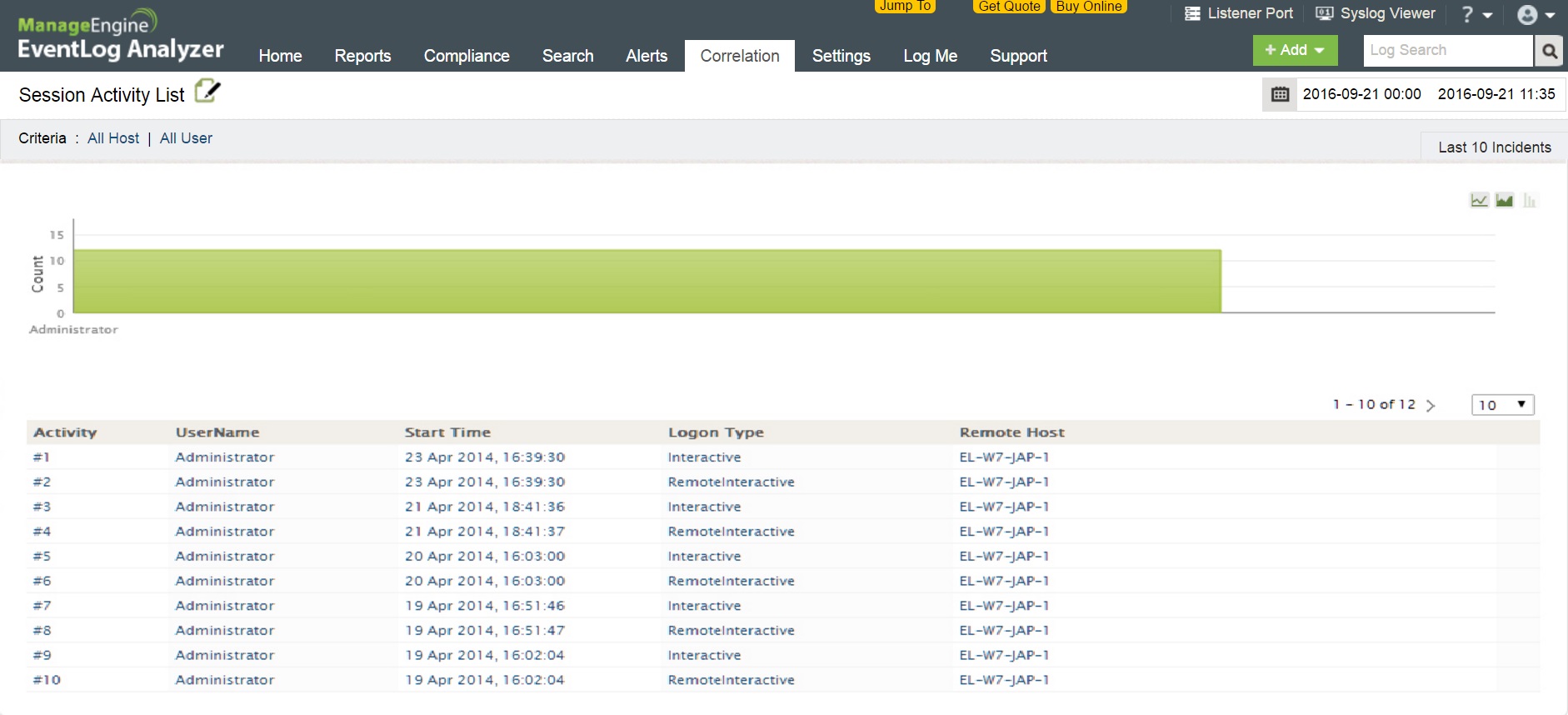
Configuring an audit log to capture database activities for Amazon RDS for MySQL and Amazon Aurora with MySQL compatibility | AWS Database Blog
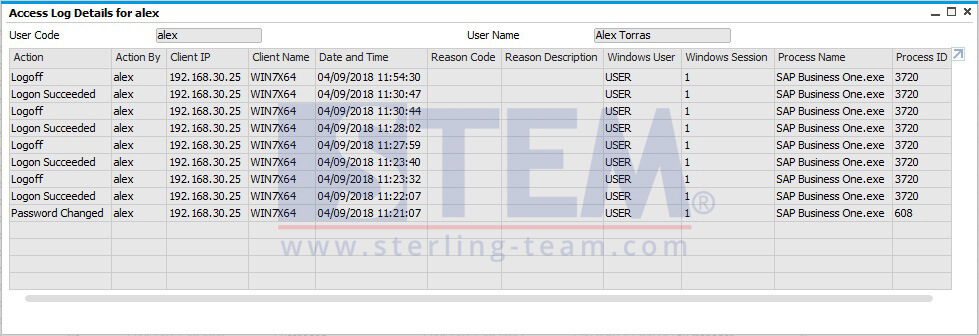
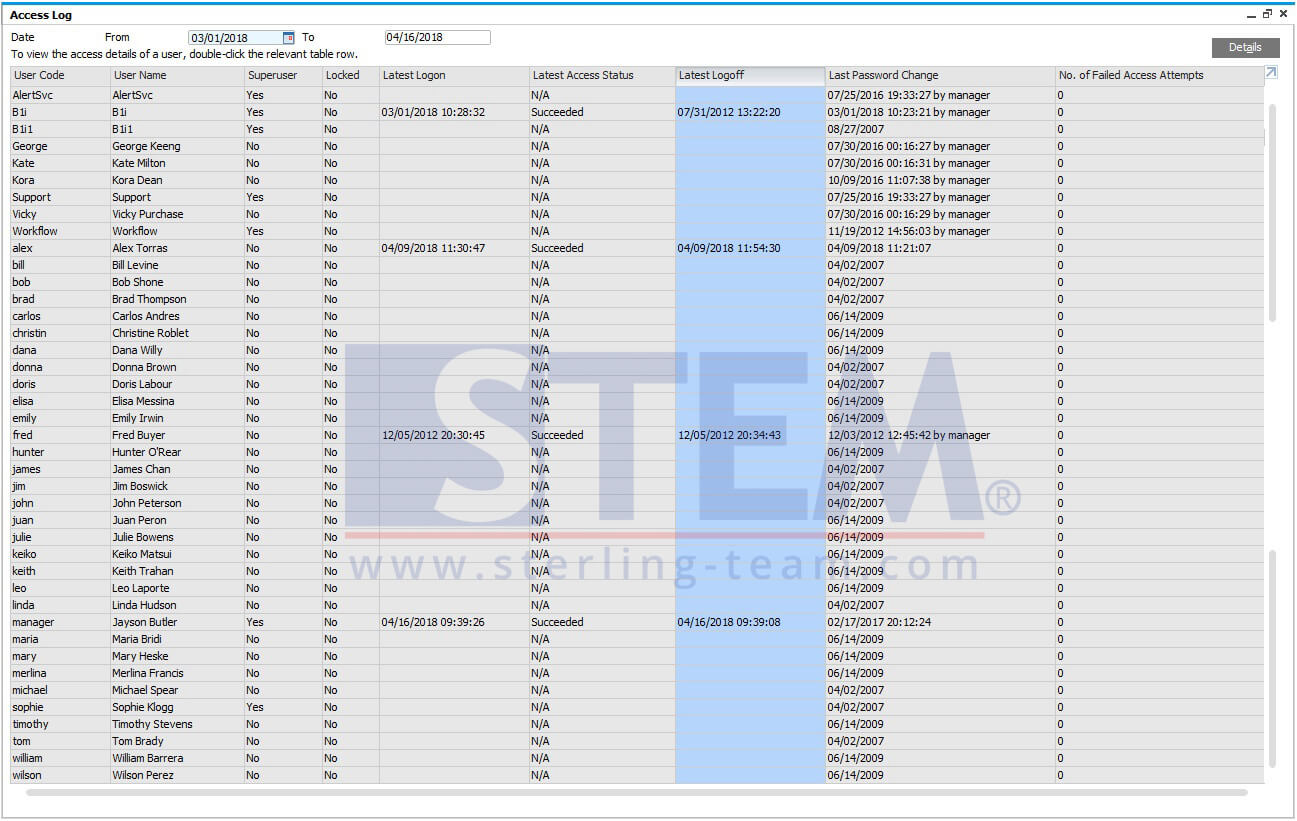
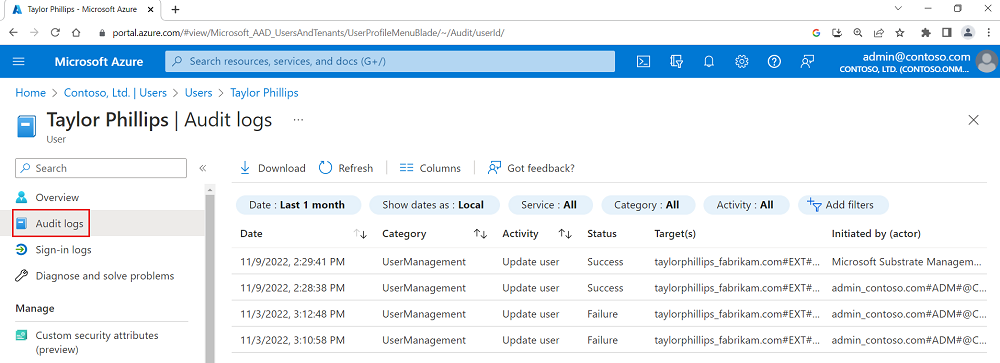
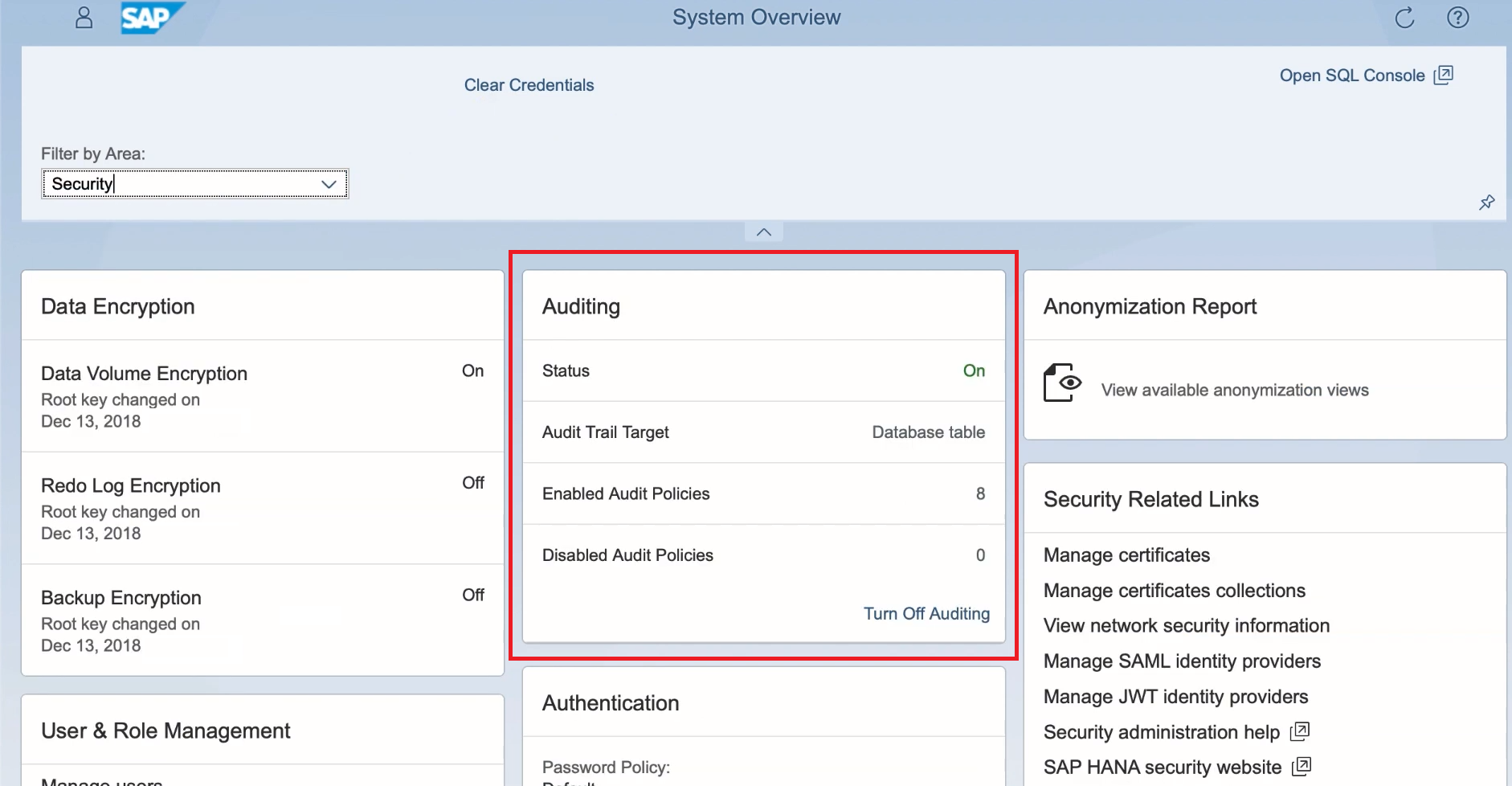
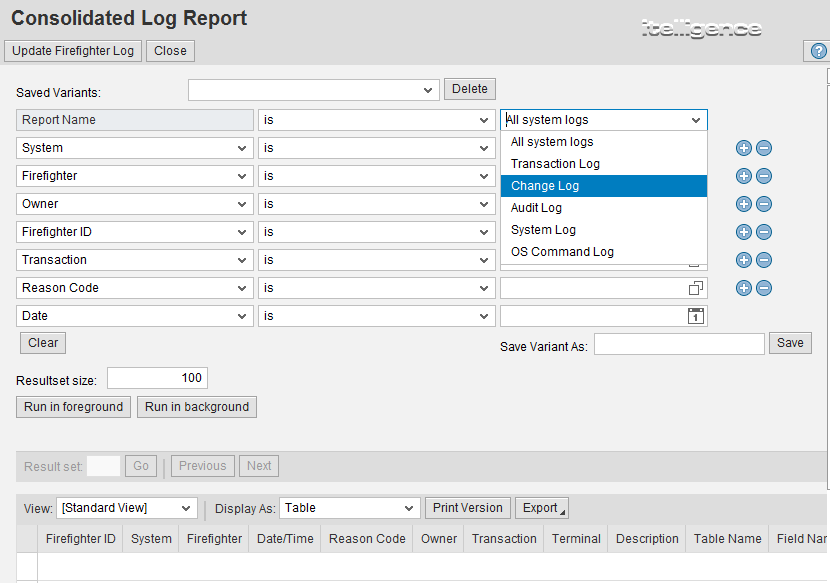
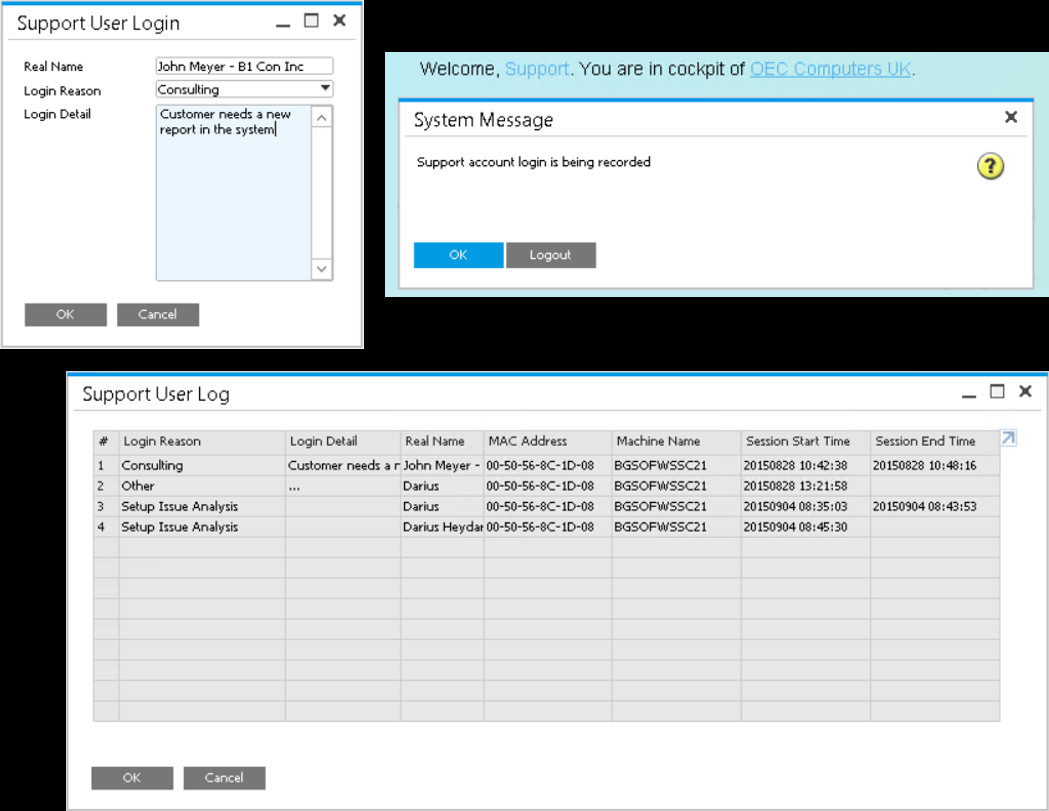
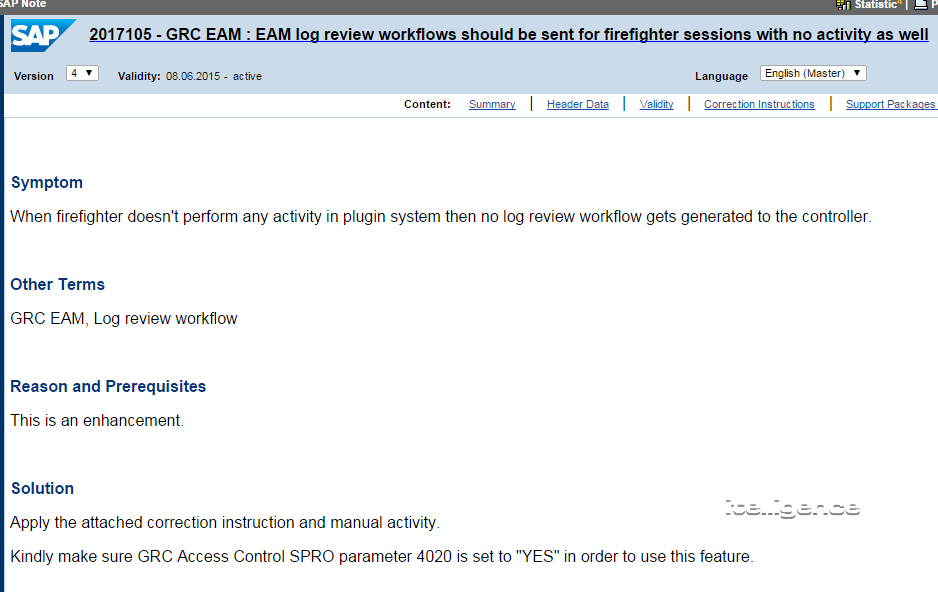
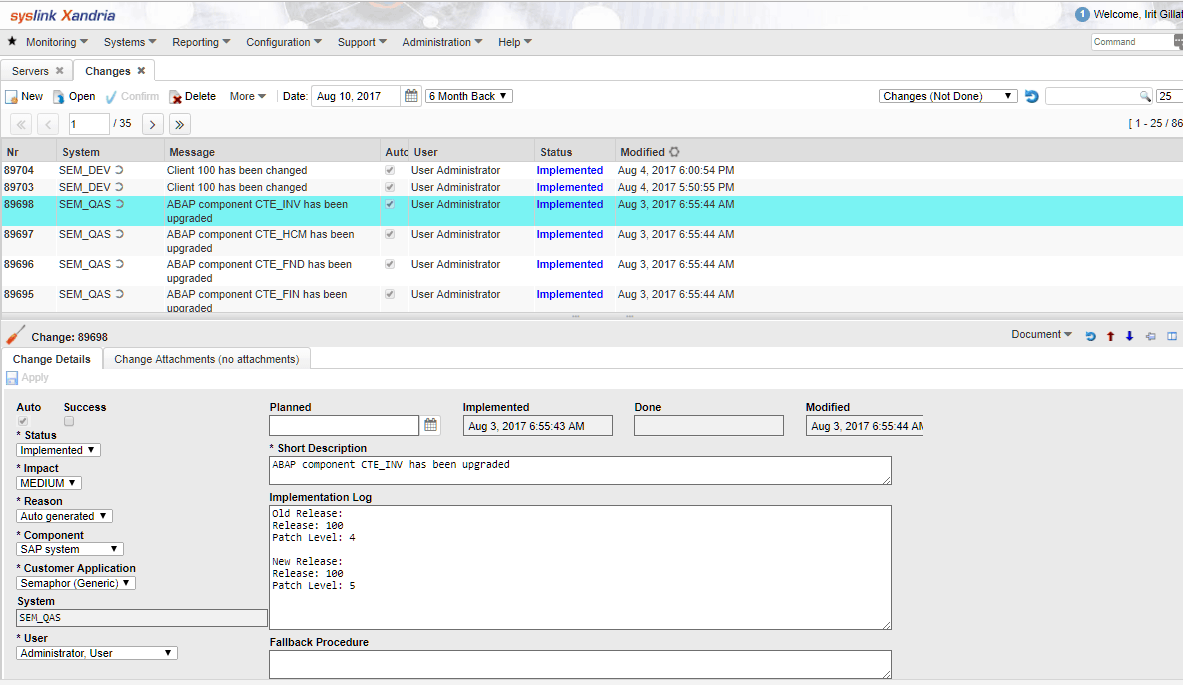
Monitoring Access Log & Change Log for Identify User Access | SAP Business One Indonesia Tips | STEM SAP Gold Partner
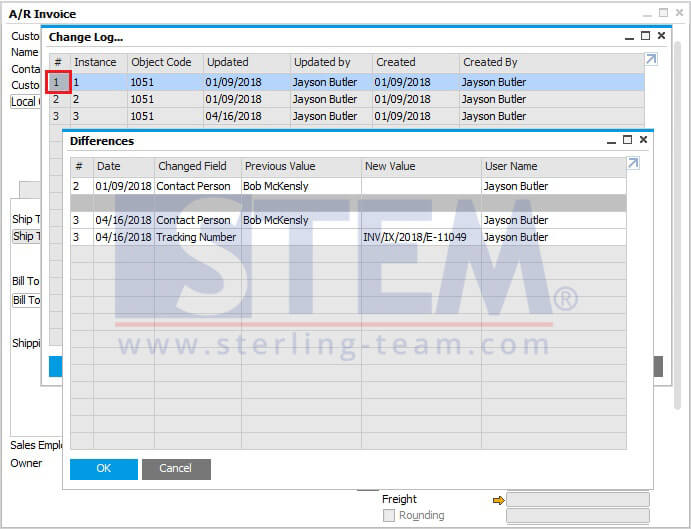
Monitoring Access Log & Change Log for Identify User Access | SAP Business One Indonesia Tips | STEM SAP Gold Partner

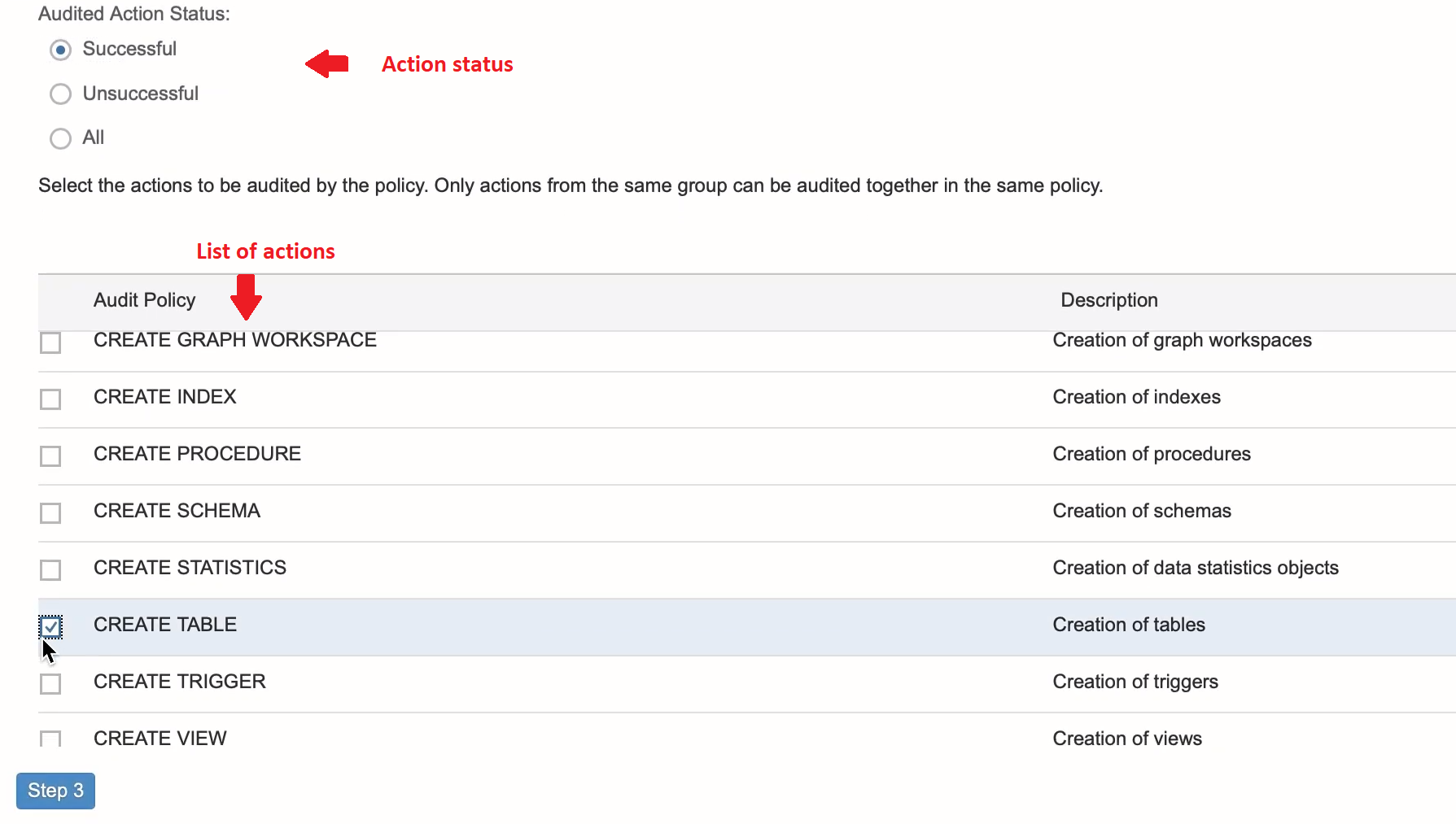
Analysis and Recommended Settings of the Security Audit Log (SM19 / RSAU_CONFIG, SM20 / RSAU_READ_LOG) | SAP Blogs